Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124

The Israeli military intensified attacks on northern Gaza on Monday, renewing questions…
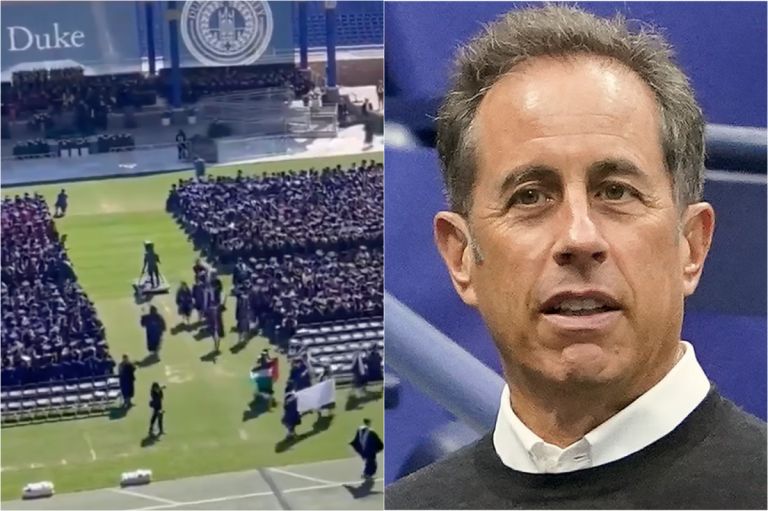
Dozens of students at Duke University walked out on Jerry Seinfeld’s commencement…

The star prosecution witness in Donald Trump’s hush money trial, Michael Cohen,…

Seattle’s restaurant community is mourning the stabbing death of a 37-year-old chef…
Dozens of students walked out on Jerry Seinfeld at Duke University as…

Jerry Seinfeld apologized for the “sexual undertones” in his Bee Movie during…

Florida’s fish and wildlife commission is searching for a boater who fatally…

Over the weekend, North Carolina experienced a rare opportunity to see the…

A man from New Hampshire has been charged after knocking over a…

Richard “Rick” Slayman, the first person to receive a genetically modified pig…

The Exton Square Mall Spring Carnival was canceled after a crowd control…

A man suspected of firing multiple gunshots at an Amazon fulfillment center…

Kansas is considering grants of up to $5 million for schools to…

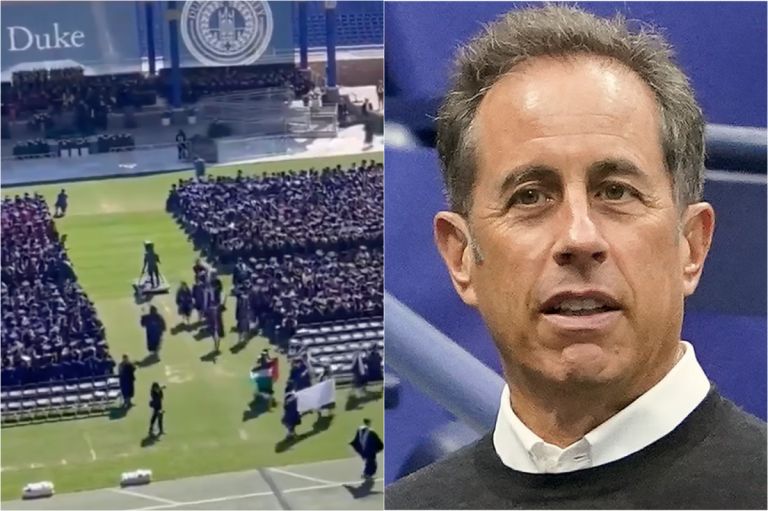
A tornado hit Finleyville, Washington County, causing destruction with trees down, homes…

Dozens of students at Duke University walked out of their commencement ceremony…

An Ohio police officer was shot and killed in Euclid after responding…

Euclid police have identified Deshawn Anthony Vaughn as the suspect in the…

The Johns Hopkins University and pro-Palestinian protesters occupying an encampment on the…

West Virginia Republicans running in the primary are avoiding acknowledging that President…

In the final hours of her U.S. Senate primary campaign, Angela Alsobrooks,…

Minouche Shafik, the president of Columbia University, was in Washington on April…

Michael Cohen, once a loyalist to Donald Trump, is now a key…

Crews are preparing to conduct a controlled demolition of the Francis Scott…

Three days after a 30-year-old mother, Brenda Duran, jumped into the San…

A mother in Georgia was fatally attacked by a pack of dogs…

President Joe Biden attended a fundraiser in Medina, Washington with other politicians,…

Donald Trump insulted the prosecutor in his New York criminal trial at…

Nicki Myers-Bates lost her mother at a young age and has been…

Three people died and three others were injured when a Tesla crashed…

Former US president Donald Trump raised eyebrows at a rally in New…

North Dakota Gov. Doug Burgum spoke before a crowd of Donald Trump…

A man in New Hampshire is facing charges after knocking over a…

Former President Donald Trump visited Wildwood, New Jersey, for a campaign rally,…

Donald Trump went to the Jersey Shore in between court appearances and…
A tornado has been confirmed in southern Allegheny and northern Washington counties,…

Jill Biden, the first lady, encouraged graduates of Mesa Community College in…

Judge Juan Merchan warned Michael Cohen to refrain from discussing the case…

Donald Trump, facing multiple felony charges, held a rally in Wildwood, NJ,…

Universities are preparing for commencement ceremonies this weekend amid pro-Palestinian protests and…

A motorcycle driver allegedly shot and killed another driver on the eastbound…

Dozens of Virginia Commonwealth University students protested Gov. Glenn Youngkin’s commencement address…
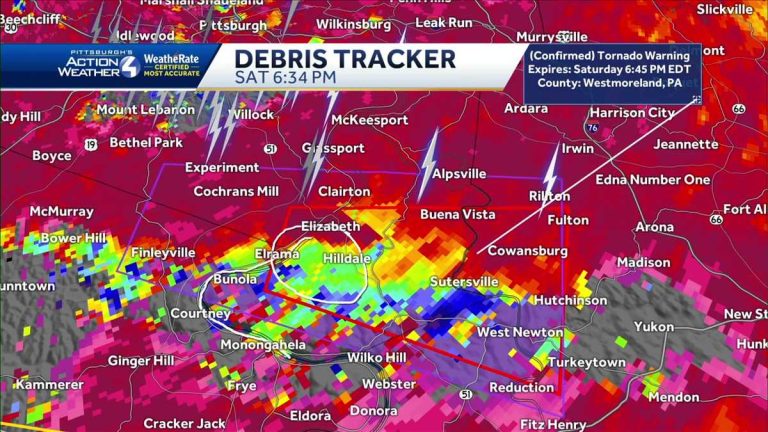
Late on April 30, Sean Tabibian called 911 reporting violence between masked…

A motorcyclist shot and killed a 19-year-old driver on the 10 Freeway…

New York City police are searching for a man who sexually assaulted…

After a cold case involving the death of University of Georgia law…

Democratic voters in Maryland’s state capital and affluent suburbs near Baltimore must…

Trump’s youngest son, Barron, has decided not to serve as a delegate…
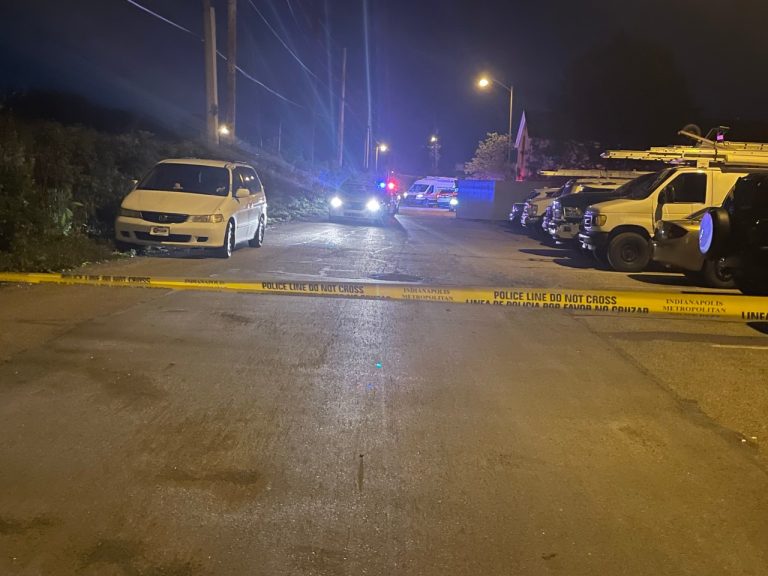
Two men were killed in separate shootings in Indianapolis early Saturday morning.…

The family of a 9-month-old baby is grieving after he was shot…

The US has expressed concerns over potential breaches of international humanitarian law…

Barron Trump has declined to serve as a delegate for his father,…

Portland State University lifted a shelter-in-place alert shortly after issuing it. They…

A federal appeals court upheld the criminal conviction of Steve Bannon for…

The USC Galen Center erupted with applause as Muslim valedictorian Asna Tabassum…

Secretary of State Antony Blinken reported to Congress on Israeli military operations…

Police made dozens of arrests as pro-Palestinian protest encampments were dismantled at…

The Biden administration acknowledges US weapons used by Israeli forces in Gaza…

A three-judge panel of the U.S. Circuit Court of Appeals for the…

The killings of Australian brothers Callum and Jake Robinson and their American…

Police in Michigan discovered a woman had been living in the rooftop…

Nearly two years after the Supreme Court eliminated the constitutional right to…

A state trooper who arrested two Philadelphia LGBTQ+ officials in March is…

A three-judge panel found Gurpreet Singh guilty of four counts of aggravated…

The Department of Defense announced additional security assistance for Ukraine, marking the…

Five Boeing 747 passenger jets previously operated by Korean Air have been…

In the hush money trial involving Donald Trump, prosecutors shifted focus to…
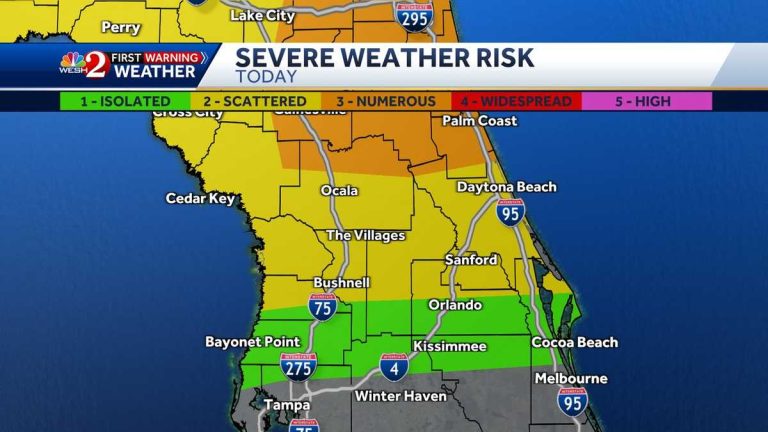
Friday in Central Florida is declared an Impact Day as two waves…

The criminal trial of former President Donald Trump in Manhattan resumed with…

Pro-Palestinian protesters on college campuses are demanding disclosure and divestment from companies…

Former President Donald Trump’s criminal trial in New York City featured testimony…

Florida police released body camera footage from a deputy sheriff who shot…

The school board in Virginia’s Shenandoah County voted 5-1 to restore the…

A Virginia school board has voted to revert two schools back to…

Former aide Madeleine Westerhout testified in court that Donald Trump would dictate…

Severe storms in Central Texas on Thursday caused significant damage in San…

Eric Trump will serve as the delegation chair for the Republican National…

The Senate passed a $105 billion aviation bill to improve air traffic…

Lawyers are challenging the sentencing guidelines in Marilyn Mosby’s mortgage fraud case…

Victoria Bencomo was shot at an Albuquerque high school graduation ceremony by…

A Florida sheriff released bodycam footage showing a deputy fatally shooting a…

Two political operatives close to Rep. Henry Cuellar have agreed to plead…

Karla Silvestre, the president of Montgomery County school board, was approached by…

Six out of the 33 individuals arrested at a pro-Palestinian encampment at…

In a recent hearing on rising antisemitism in schools, school leaders and…

A Florida sheriff’s office released bodycam footage from a deputy who fatally…

The fate of a major federal aviation bill is uncertain in the…

Alabama has scheduled the upcoming execution of Alan Eugene Miller, a convicted…

A New Hampshire man, Adam Montgomery, is being sentenced for the murder…

Attorneys are pushing for the release of P.G. Sittenfeld, who is currently…

Australian surfer Callum Robinson, 33, was murdered in Mexico while traveling with…



